Amber: Rewriting Comfort in Bash — Promises and Pitfalls of a Universal Transpiler
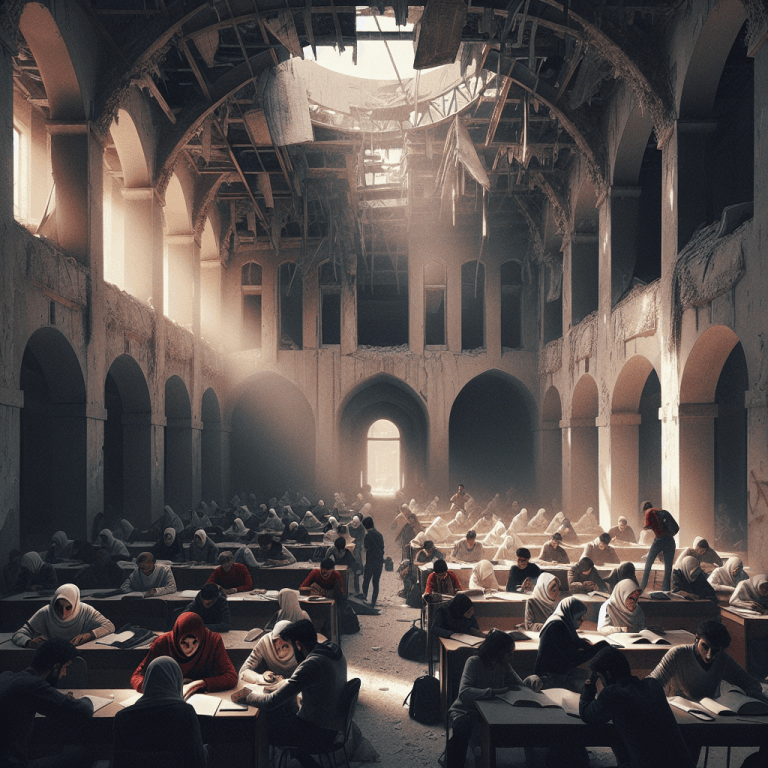
Why Bash Still Reigns, Even When It Hurts
Bash is everywhere: on cloud servers, inside minimal containers, on developer laptops and in boot scripts. That ubiquity explains why teams continue to rely on it at scale, even for tasks where more modern languages would be preferable. The uncomfortable truth is that Bash combines near-universal portability with a syntax that rapidly becomes unreadable, fragile in the face of whitespace and quoting, and prone to security issues such as injection, unexpected globbing, and word-splitting.
Amber: a Friendlier Front End Over Bash Minefields
Amber promises to preserve Bash's portability while offering a more readable syntax inspired by higher-level languages like Python. Demonstrations at FOSDEM 2026 showed how Amber transpiles concise, expressive source into longer POSIX-compatible shell scripts that can run almost anywhere. Public examples highlight cleaner constructs: explicit function declarations, symbolic primitive types (for example, Num), iterable loops, safer string concatenation, and preflight dependency checks via an auxiliary tool, bshchk.
What a Transpiler Actually Changes: Ergonomics or Illusion?
The Amber proposition is straightforward: provide a modern development experience — less boilerplate and fewer quoting headaches — while emitting an artifact that requires no additional runtime beyond Bash. That sounds ideal for constrained environments (alpine containers with Bash installed, systems limited to /bin/sh-compatible shells, or infrastructures where adding interpreters is disallowed). However, the advantage carries trade-offs. Source written in Amber must be reliably mapped to Bash in a way that preserves program logic and security guarantees. Imperfect mappings degrade debuggability and traceability, and subtle behavior changes can surface only after transpilation.
Where Amber Can Become Indispensable
Amber deserves serious consideration in specific operational contexts: provisioning scripts and lightweight DevOps tools that benefit from improved readability; installers and deployment kits distributed across heterogeneous environments; and CI/CD automation that must be replicated across many minimal images. In these scenarios, a clearer, more expressive syntax reduces human error and accelerates authoring. Amber also enables teams to maintain a single source of truth: write in Amber, distribute the transpiled Bash artifact.
Invisible Dangers: What Can Go Wrong
Transpilation introduces complexity. The generated Bash is often longer and more intricate than the Amber source, making manual fixes harder. In critical operations, an administrator unfamiliar with Amber must either learn the Amber source or audit the generated Bash, effectively doubling maintenance effort. Technical risks include hidden external dependencies: Amber may emit calls to utilities absent on a target system. Tools like bshchk can surface such gaps, but their use must be mandatory in release pipelines.
More concerning is shell diversity. Not all systems use Bash as /bin/sh; many distributions ship dash or other, stricter shells. Amber's roadmap mentions zsh support, which underscores a persistent mismatch between transpiler output and the diversity of real-world shells. Complex generated code can also introduce quoting and execution vulnerabilities that evade simple review; without automated auditing, these issues are easy to miss.
Why Not Just Use Python or Go?
The counterargument to adopting full-fledged languages remains valid: Python and Go bring runtimes and dependencies that may be absent in minimal systems; container images grow larger; and policy or operational constraints sometimes forbid installing anything beyond the system shell. Amber aims to deliver high-level ergonomics without sacrificing runtime compatibility. That said, where Python or Go are available and permitted, their mature tooling, libraries and testing ecosystems often make them the safer choice. Amber's sweet spot is teams that explicitly want a lightweight DSL for scripting while retaining the universal deployability of shell scripts.
Practical Rules for Adopters
1) Treat Amber as a development aid, not a magic bullet: keep the generated Bash artifact in the repository or the release pipeline so the deployed artifact is always auditable. 2) Make bshchk usage mandatory in CI to detect missing utilities and platform mismatches early. 3) Run unit and integration tests against both Amber sources and the transpiled Bash to catch transpilation discrepancies. 4) Require security reviewers to inspect the generated Bash; do not assume the transpiler eliminates all quoting and exec-related risks. 5) Define a clear support policy: who fixes Amber source, who debugs generated Bash, and how rollbacks are handled.
Signals for the Community and Next Steps
Wider Amber adoption will hinge on ecosystem investments. Essential tools include linters for Amber syntax, editor and IDE integrations, stack-trace mapping between generated Bash and Amber source for debugging, and automated auditors for common shell pitfalls. Community contributions that harden the transpiler and extend compatibility across diverse shells will be decisive. FOSDEM provided a positive early spotlight; broader, organized efforts around testing matrices, cross-shell compatibility, and third-party audits will determine Amber's viability beyond enthusiasts and small platform teams.
The Warhial Perspective
Amber arrives amid a search for balance between portability and developer productivity. Its core promise — write modern code, deliver Bash — resonates strongly with DevOps teams operating in constrained images where adding runtimes is impractical. Yet syntactic elegance alone will not guarantee success; adoption is as much a social challenge as a technical one. Administrators and security teams must be convinced that Amber artifacts are safe, reproducible and transparent. Complementary tooling — linters, debug mapping, and automated audits of generated scripts — is not optional but essential if Amber is to bridge the trust gap.
Forecast: over the next two to three years Amber is likely to find traction in small projects and platform teams that need portable, readable scripts that are quick to author. If Amber's maintainers prioritize strict /bin/sh compatibility, robust tooling for audit and dependency checking, and clear guidance for operational workflows, adoption could broaden. Without those investments, Amber risks fragmentation: a wave of internal projects that author in Amber but ship only the transpiled Bash, leaving system administrators to treat Amber as an obscure internal tool rather than a standard part of system administration practice.